Three lawsuits were filed at the end of March in the United States District Court for the District of New Jersey against Monmouth University alleging that the university failed to protect highly sensitive data and allowed cybercriminals unrestricted access to their students’ and employees’ personal identifiable information (PII).
The Plaintiffs are Jordan Staub, Erin Masterson, and Matthew Englehardt, all former Monmouth University students, all a part of the class action lawsuit. According to Masterson’s complaint, her case is a class action with 100 or more members of the proposed class and at least one is a citizen of a state different from the defendant. Claims of all members of the proposed class are in excess of $5 million.
Only a few years ago, Monmouth was faced with another class action lawsuit unrelated to this cybersecurity incident. In 2022 Monmouth University agreed to a $1.3 million class action settlement to resolve claims that it failed to refund students for on-campus tuition during the COVID-19 closures, according to Top Class Actions. The class action lawsuit sought refunds for excess tuition. Students claimed to have overpaid because the university transitioned to remote learning in March 2020 and were no longer living on-campus, using on-campus resources, or participating in student organizations.
For this current incident, the lawsuits are mounting. We reached out to Charlene Diana,Vice President and General Counsel, and sought to find out about the legal repercussions of such cyberattacks. In addition, we sought to understand potential repercussions that class action lawsuits might have on the university. She provided us with the following response, “I am not able to provide comment on any potential or ongoing litigation related to this matter. Our current focus is on addressing the incident at hand and providing support to our community members.”
Masterson’s complaint alleges that, “Defendant has not informed its current and former students and/or employees [as of yet] of the Data Breach. Indeed, Plaintiff and Class Members were wholly unaware before posts about it began appearing on the Dark Web, including the publishing of their PII.” President Leahy informed current students and employees about the data breach via email on March 13. As of the writing of this article, we were not able to independently confirm whether or not former students were informed of this incident. John Sonn, Associate Vice President and Chief Information Officer stated that the university is working on identifying individuals who have been affected by the data breach. “As a part of our investigation and response, we are working to identify the specific information that was involved so we can notify any individuals that had their personal information included. We are committed to transparency and keeping our community informed, and appreciate their patience and understanding as we conduct our investigation. As we move forward, we are working with our cybersecurity experts to further enhance the security of our systems to prevent a similar incident from re-occurring in the future,” he said.
New Jersey Identity Theft Prevention Act requires universities’ disclosure of data breaches to be done “expediently and without a reasonable delay.” In the case that PII is compromised the university must notify the affected individuals and the New Jersey Division of State Police. On a federal level, Gramm-Leach-Bliley Act (GLBA) requires universities that participate in Federal Student Aid programs to report data breaches to the Federal Student Aid (FSA) office within 24 hours after the incident is identified.
The Outlook asked Sonn, specifically to provide his assessment of Monmouth’s cybersecurity preparedness. He provided us with what he called “our” official statement. The statement is as follows, “Monmouth University recently discovered a cybersecurity incident that occurred on our systems which resulted in the unauthorized access to some information on our network. Upon learning of this incident, we immediately initiated our response protocols, engaged cybersecurity experts, and notified the FBI and the Department of Education. We believe the incident has been contained. Importantly, there has been no operational disruption, and University systems and programs continue to operate as normal.”
In our last coverage of this incident, we informed the campus community that the perpetrator was Pear Extraction and Ransom (PEAR) who claims to have stolen 16 terabytes of data according to Comparitech. PEAR is alleged to have stolen included but not limited to financials, students’ private and confidential data, PII, Protected Health Records (PHI), minors data, files from OneDrive and Dropbox Cloud storages. Masterson’s filing specifies that the PII’s stolen include “names, addresses, phone numbers, emergency contact information, insurance information, financial information, partners’ and vendors’ data, students’ private and confidential information including grades, email correspondents, and university HR records which could potentially include personal health information.” According to Health and Human Services, in cases in which the university maintains health records that are not part of an education such as those in a campus health center for treatment purposes, it may be subject to HIPAA’s Breach Notification Rule by which affected individuals must be notified without unreasonable delay and no later than 60 days following discovery. In case the breach affects more than 500 residents of a state, the institution must provide notice to media outlets.
President Leahy’s email from March 13, informs that cybersecurity experts and law enforcement were engaged to assist in the investigation. He offered general information to students and employees about the steps they can take to protect themselves from misuse of personal information by offering a link to consumer advice available on the Federal Trade Commission (FTC) website. According to Staub’s filing, FTC updated its publication, Protecting Personal Information: A Guide for Business, in 2016, in which it states that FTC brings enforcement actions against businesses for failing to protect customer data adequately and reasonably.
The lawsuits allege that Monmouth University failed to follow minimum industry standards and cybersecurity measures putting students and employees at risk. In Staub’s filing, it is alleged that Monmouth University failed to train its employees on cybersecurity and failed to maintain cybersecurity safeguards and protocols. Englehardt’s filing states that Monmouth University lacked, “effective means to protect, detect, stop, or mitigate breaches of its systems.” As a result, as stated in the lawsuit, it is not known how much time cybercriminals had access to Monmouth data before the breach was discovered. President Leahy, in his March 13 communication, said that the university acted “immediately after becoming aware of the incident.” “We initiated our response protocols and engaged cybersecurity experts and law enforcement to assist in our investigation of this matter, including a thorough review of the data/information that has been accessed,” he said.
Lawsuits further allege that this behavior was both reckless and negligent. In Masterson’s filing it is stated, “Defendant disregarded the rights of Plaintiff and Class Members by intentionally, willfully, recklessly, and/or negligently failing to implement adequate and reasonable measures to ensure that Plaintiff’s and Class Members PII was safeguarded, failing to take available steps to prevent unauthorized disclosure of data and failing to follow applicable, required and appropriate protocols, policies, and procedures regarding the encryption of data, even for internal use.”
Danny Crawford, a computer science major, shared his concerns about this data breach with the Outlook. Crawford was concerned about the amount of information that’s been reportedly taken and how his personal information might be used including his credit card information. He said, “…there is a lot of private information that the university stores that can be exploited…that’s why when you have a security breach with a database that involves social security numbers, date of birth, even health information, that’s really bad.” Crawford was concerned that many in the Monmouth community aren’t understanding the scope of this breach. As far as the university’s response he shared some criticism, “I feel like it is getting swept under the rug and not taken as seriously as it should be…that is the scary part about this, it is getting so downplayed when it’s really serious.”
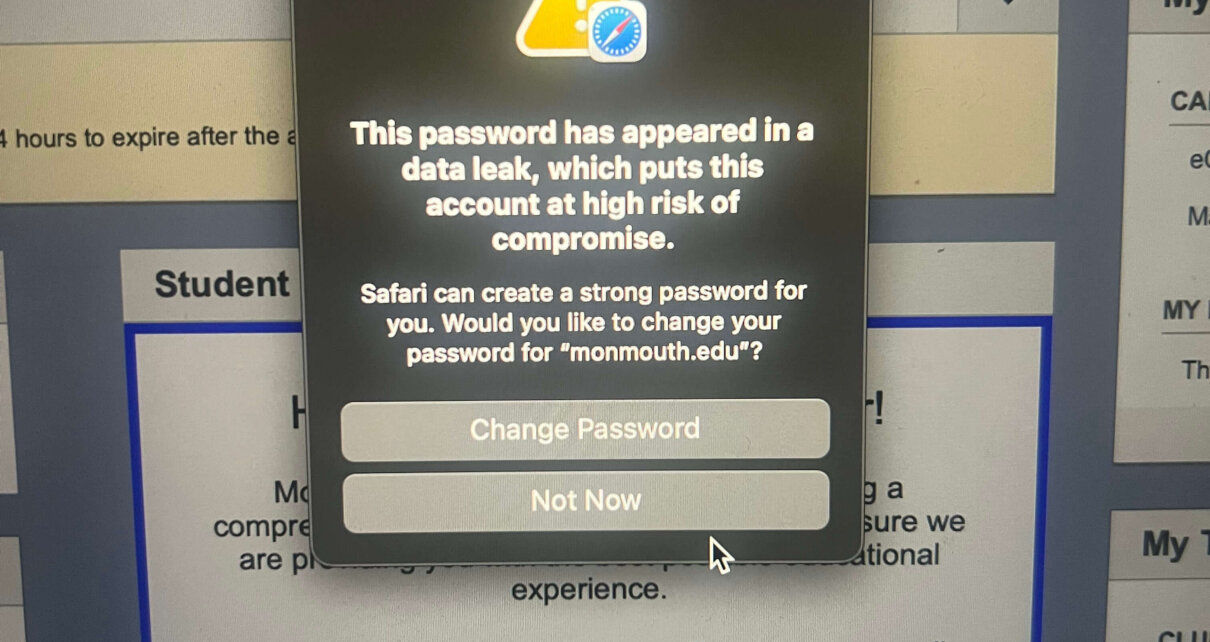
Another student who wished to stay unidentified in this story shared their concern about their data being leaked to the Dark Web when they noticed a pop-up window upon their login into their Monmouth email that read, “The password has appeared in a data leak, which puts this account at high risk of compromise.” “I’m not sure if this notification is linked to the cybersecurity incident, but it made me nervous and worried that it might be, I have no way of knowing,” they said.
As this has been a developing story with high impact on students, employees, and alums, we reached out to President Patrick F. Leahy for any updates on the incident. “We continue to partner with our external team of cybersecurity experts as part of our ongoing investigation and response. Once we have new information to report on the specific data that was involved, we will advise the university community and notify any individuals that have been impacted,” he stated in an email correspondence. “In the meantime, if our community members have specific questions or concerns, we encourage them to contact support@monmouth.edu directly. The senior administration and I extend our thanks for the continued patience of our university community while the investigation continues in earnest,” he added.